When I first heard about Meraki years ago, one of the coolest features I saw that the access points supported was automagic Mesh Routing. I was a little more naive back then so I didn’t pay it much attention, and technically speaking it is still a cool feature. However, with it being a feature, one would think that it could be disabled, but I found out that it can’t be disabled. Ever…apparently. Now this might not seem like a big deal (and maybe it isn’t), but I’m a stickler for how I want my wireless to operate.

Follow me along on this quick adventure of how I discovered this, and why I don’t like it. ^_^
I was in the middle of deploying a new site with some fresh MR32 access points. I had setup a simple Open SSID for quick access, and configured the SSID with Band-Steering enabled.
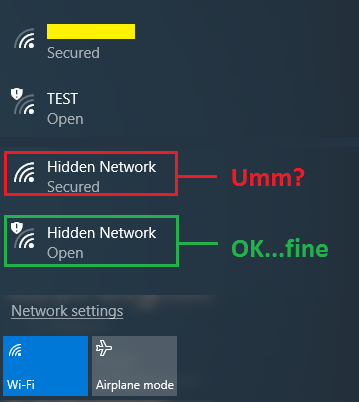
This site is in the middle of nowhere, and nothing else is around from a wireless perspective. I then noticed something unusual on my Windows 10 laptop, two hidden SSID’s, one with security and the other Open. I thought “that’s strange”, because my access point is the only one powered on for miles around.
I know that when you enable Band-Steering, the Meraki access points will tweak the 2.4GHz Beacon frames so that they show up as hidden. This is one of the methods Meraki does to persuade dual-band clients to connect to the 5GHz radio. I’m not particularly a fan of this, but meh.
So I’m expecting to see the ‘Hidden Network’ that has Open authentication, but I was not expecting to see this ‘Hidden Network’ that is Secured.
So of course, I’m naturally curious as a kitten as to what the hell this is. I fired up a second MR32 so I could test to see what was going on. I changed my Open SSID to PSK to see what affect it had. The Open Hidden Network changed to a Secured one. I can’t seem to find any rhyme or reason to when or how the Mesh Routing SSID becomes visible, because testing this in my lab I was unable to duplicate these findings. My best guess it is is firmware based.
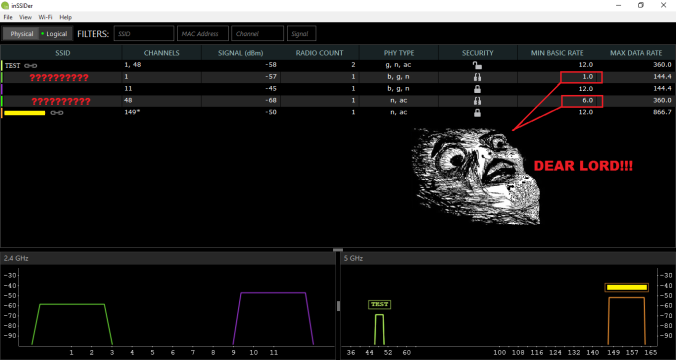
I setup a new SSID called TEST and made that Open Auth.
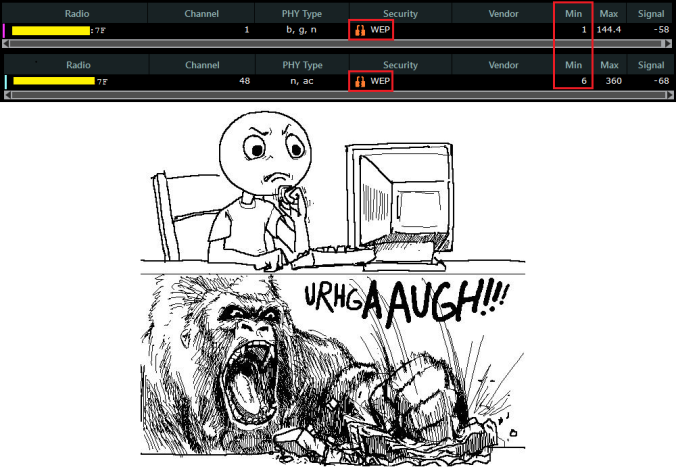
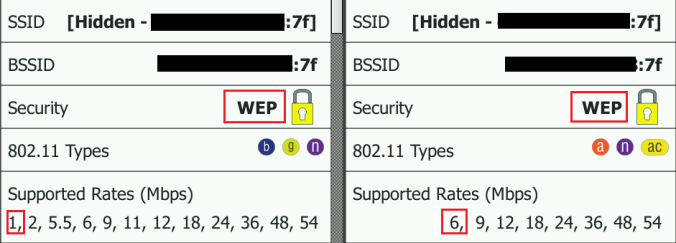
I have both SSID’s set to have 12Mbps as the lowest Mandatory Basic data rate. I fired up inSSIDer to get a quick view of what is happening. I see TEST on channels 1/48, and my other SSID on channels 11/149.
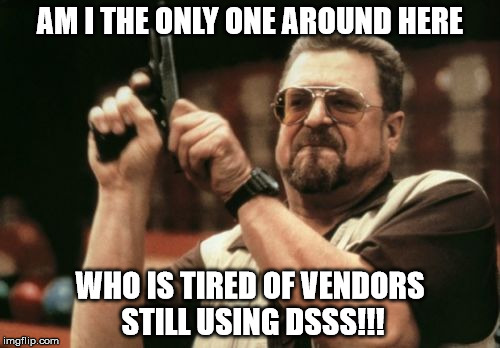
The problem I see is that inSSIDer is detecting 5 SSID’s, instead of the 3 I was expecting. What is worse, is that those 2 extra unknown SSID’s are using the lowest possible data rates per band (1Mbps, and 6Mbps). This surely can’t be coming from my access points, because I have the mandatory basic rate set to 12Mbps.
I checked the radio MAC addresses of the 1Mbps and 6Mbps Hidden SSID’s, and low and behold they match that second MR32 that I have the TEST SSID running on. How can this be !!!!!! RAWR
Want to make this situation even worse?
IT’S USING WEP Encryption !!!
I thought maybe inSSIDer was messing up, so I double check on my NetScout G2, but alas, the facts don’t lie.
So…something is going on here. Time to call Meraki support to try and find out.

In all seriousness though, the support line at Meraki is actually phenomenal, and I’ve never had any issues reaching out to them. =)
The information I got back from Meraki, is that the HIDDEN WEP SSID is the Mesh Routing between the access points, and it by default sends at 1Mbps for 2.4GHz and 6Mbps for 5GHz, to ensure it can go as far as possible. As to why it is using WEP encryption, I could not get a straight answer. They did claim that this was a ‘new thing’ that just came out with their latest firmware version, so when I had them rollback to the previous build, I did not see any of this.
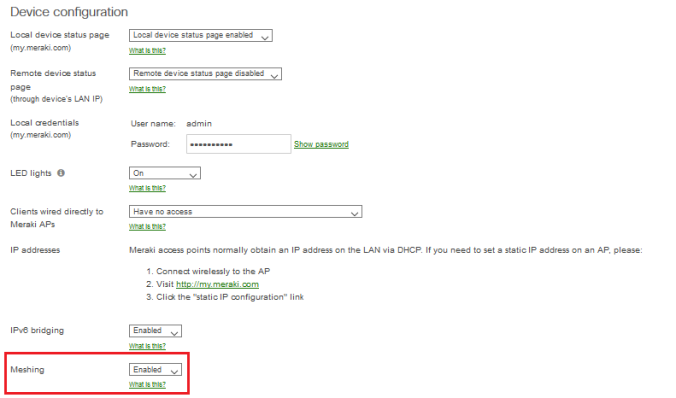
The Meraki engineer told me that they have a hidden GUI feature where I can turn off this Mesh feature, which was perfect. I have no use for any AP being in repeater mode, as they are all cabled, and I have no use for 1Mbps existing anywhere in my world.
He enabled the feature for me and told me to go to Network-wide>Configure>General and I should see it under Device Configuration. And boom, there is it.
I quickly set it to Disabled, and went back to my sniffing to ensure it worked. This is where my heart gets broken. I still see those 1Mbps frames. I call Meraki back and as it turns out, this Meshing feature will only disable the access points going into repeater mode, and it does not actually stop them from sending out their 1Mbps WEP Hidden special Mesh Routing nonsense.
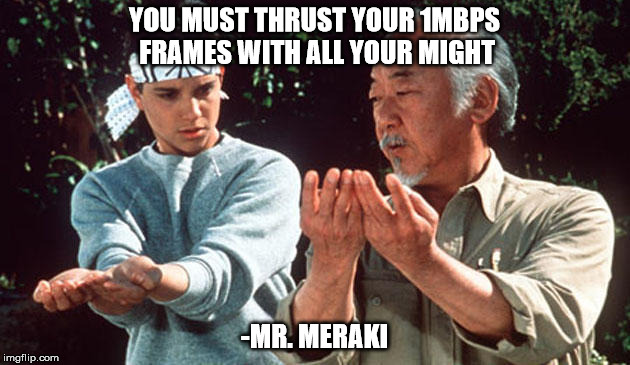
So I’m stuck with it. There isn’t anything I can do to disable this, because it’s somehow built into the firmware’s firmware, which cannot be undone. They gave me something along the lines of, “No matter how hard the wind howls, the mountain cannot bow to it”.
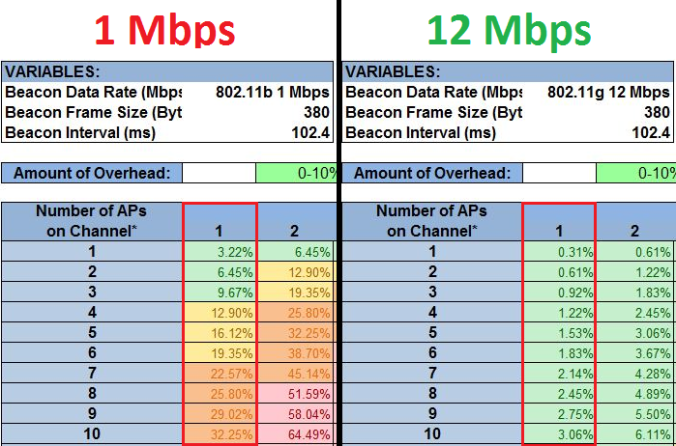
So since there is nothing I can do, I was at least curious to see how much unnecessary overhead this is going to be giving me. I fire up Savvius Omnipeek to take a gander.
The only two frames I see are Beacon frames sent every 102.4ms (as usual), and SNAP Header broadcast frames sent at random intervals with no apparent pattern and no real data to digest (roughly 30 frames every minute). I asked Meraki what it was about, but they said the details are top secret and cannot share them. All they could tell me was that the Meraki Mesh Routing was based on RoofNET.
So since its basically mostly only sending Beacons, what I do know is based on my hero Andrew Von Nagy’s SSID Overhead calculator, we are looking at a single SSID at 1Mbps and its basically a complete and unnecessary waste of my airtime (see what I did there?), that I can’t do jack diddly squat about.
I hope that one day Meraki will give us the power to disable this.
If you feel I’ve gotten anything wrong with this post, please by all means feel free to educate me.
**UPDATE as of 5/23/2017**
Not sure when the change happened, but Meraki appears to have heard our cries and disabling MESHING actually now does indeed kill all MESHING communications. Hurray !
Thanks!
-Nolan


Is Meraki creating a hidden SSID for Meshing per SSID that you create? Lastly, if we assume there is only 1 access point and if you create a new SSID, does Meraki AP put it on a non-overlapping channel per SSID that you create? I thought all SSID’s would be on the same channel. I am guessing it depends on the number of radios your access point has and if you are doing channel bonding right?
LikeLike
As far as I can tell it is only one unique hidden SSID in total, not per my own SSID count. That would really hurt things. The channel the ‘mesh ssid’ operates on is still tied to the channel that the AP is using. I would imagine it goes off-channel to find other nearby access points that are not running the same frequency, kind of like NDP with Cisco. I haven’t really dug into the details of how it operates. I figure its still doing its mesh behind the scenes even if you don’t have any SSID broadcasting. There is a good deal of mystery to it, cause I don’t always see the ‘mesh SSID’, so I’m not sure if its actually on or off.
LikeLike
Love this post A++++
LikeLike
I noticed the same results that you mentioned in your blog. Was doing some digging and found this:
https://documentation.meraki.com/MR/WiFi_Basics_and_Best_Practices/Mesh_Networking#Meraki_Mesh_Algorithm
According to this they should be doing AES. I wonder if something changed since they wrote unless I’m reading it wrong?
LikeLike
In case anybody is curious, the hidden SSID is “mesh” for that WEP network. I wasn’t sure what it was, so I ran mdk3 against it in brute force mode. Only took a few minutes.
I really hope they’re just encapsulating whatever traffic is being meshed with WEP, but that the actual traffic has some kind of IPSec applied to it. I’m going to give them the benefit of the doubt here but I do look forward to somebody else (who has the time) digging into this.
LikeLike
Needs to have the ability to shut it down.
LikeLike
sounds like a good defcon talk
LikeLike
Thanks so much for this post! I have been fighting with these radios for a year. I just keep going back to old firmware and when they update, I forced them to send me back again….lol. It caused lots of performance issues with our very dense environment. They assured me I was crazy of course I have already emailed them to have the setting enabled in our GUI. Cheers!
I have already emailed them to have the setting enabled in our GUI. Cheers!
LikeLike
I like this post and it’s really practical.
LikeLike
This post is awesome. Just wondering if the hidden mesh SSIDs have returned after more firmware upgrades in the summer. Also curious if this applies to newer Meraki products, MR34, MR42 etc.
LikeLike
Yes they still broadcast on new firmware. They swear that it doesn’t cause a problem, however I beg to differ. I spent weeks going back and forth with them on this issue and the issues they were causing us with AirPlay. Finally got the to downgrade our firmware version to 2311. Amazing…..now everything work beautifully again. This is the last firmware available before the radios get turned on. Good luck….they are reluctant to do so as that firmware is not supported any more. I think the idea is great…..But allow us to turn it off…….
LikeLike
Nate – what issues were you having with AirPlay? We are having some issues too, and are trying to figure out what is going on…
LikeLike
With the latest WPA2 hack, Meraki claims that mesh networking is not impacted. Do you think it is because meraki devices are using WEP instead of WPA2. In that case, it would be extremely misleading and exposure to Meraki mesh would be even bigger than WPA2. Can you confirm Nolan?
LikeLike
it’s all marketing speak – “No we are not affected by the krack vulnerability” (me finishing the sentence for them) because we are not using WPA2 or any strong encryption for that matter.
LikeLike
Thanks for taking the time to write this article Nolan! We had a similar issue with our network and the support with Meraki is going nowhere. After we found your article, we ask Meraki to give us the ability to turn off our meshing capability and WEP is gone now.
LikeLike
You sir, are a saviour! This blog post helped me a great deal.
LikeLike
Great post. Does this explain why a couple of my AP’s are automatically saying they are “Good Repeater” modem even though all of my AP’s are wired to the same set of switches?
LikeLike
These hidden SSID’s, anyone noticed that they have the network name, longitude and latitude where the devices are located. Recently was doing some captures and found that out.
LikeLike